AKM eliminates endpoint breaches
Why Choose AKMSecure?
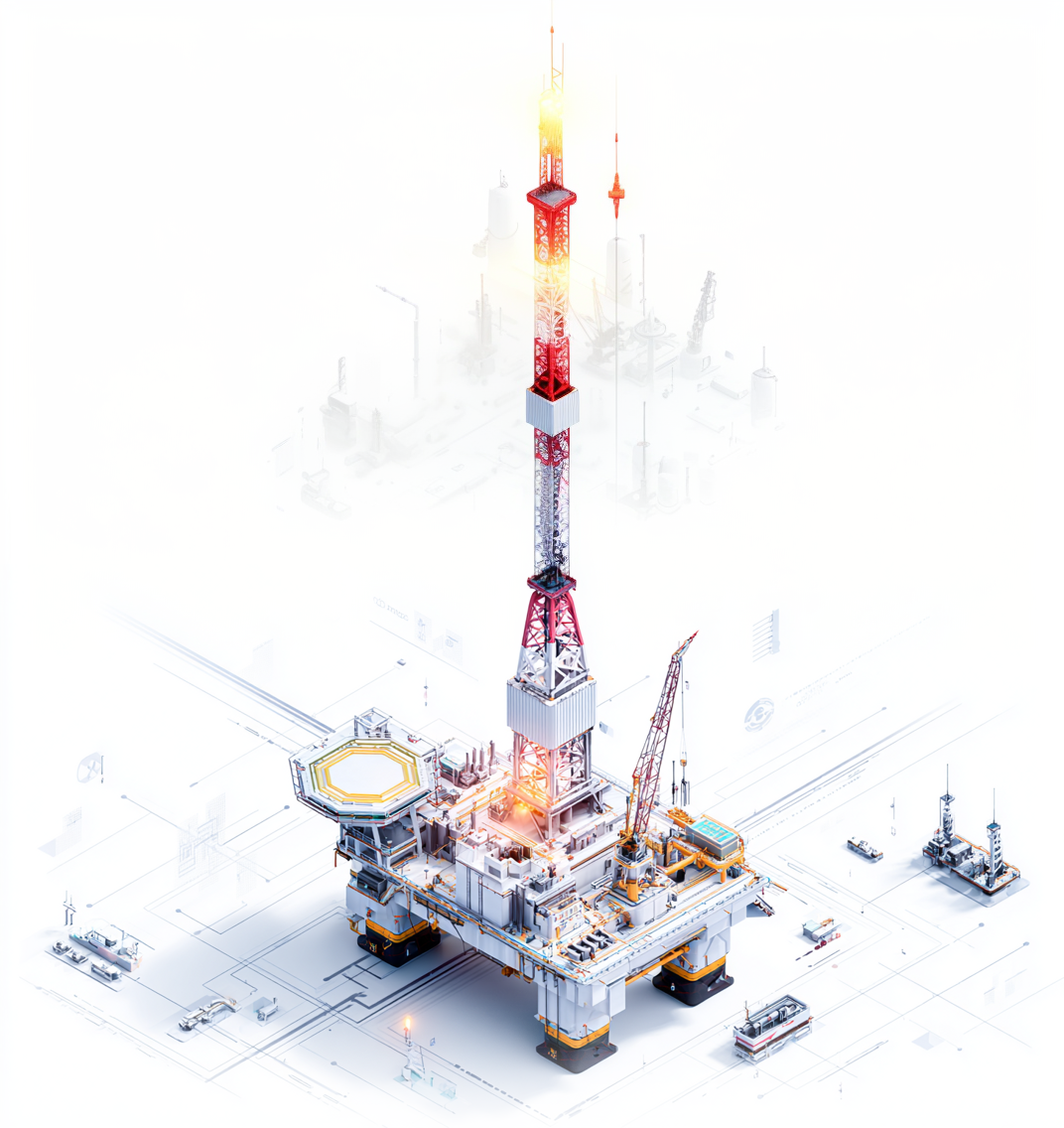
Built for the Future of OT Security
AKM isn't just a better product. It's a better philosophy:
Trust nothing. Automate everything.
Secure by design.

Patent-Backed Security
Four patents power our unique approach to Autonomous Key Management (AKM)
High-Performance Codebase
C-based, modular components under 10KB — optimized for embedded and air-gapped systems
One-Time Setup
Fully autonomous and self-optimizing, with no ongoing manual input
Compliance Ready
Aligned with EU and global cybersecurity mandates like IEC 62443 and NIS2
Our Story
A Next-Gen Security Model, Born for the Edge
AKM was created by engineers who saw how traditional PKI security models were failing the systems that matter most — not laptops or apps, but power grids, pipelines, satellites, and hospital devices.
Rather than patch PKI for OT, we started from scratch.
We're redefining operational cybersecurity with a next-gen platform for critical infrastructure defence, manufacturing and beyond. Our mission is simple: Protect the systems that power our world — without relying on the cloud, manual input, or assumptions that breaches are inevitable.
ZERO TRUST
isn't a buzzword.
It's built in.
Quantum Resilient
Framework that authenticates every connection
One-Time Setup
A set up that runs forever without manual input
Implicit Zero Trust
A system that delivers implicit Zero Trust, by default, with every frame
10KB Footprint
Architected server/client multitrack applications for broadcasting
How We Solve The Challenge
OT Cybersecurity Is Broken
Industrial systems are under siege. Attacks are increasing 30% year over year, causing more than $10 billion in annual damage. And yet, most cybersecurity solutions still rely on outdated Public Key Infrastructure (PKI) — too complex, too manual, and completely unusable in air-gapped or resource-constrained environments.
As regulators demand security by design , organizations are stuck choosing between fragile legacy tools or risky cloud dependence.
Unbreakable Autonomous Key Management (AKM) for Air-Gapped ICS
Secure disconnected OT environments with AKM (Autonomous Key Management) SecureKey. Generate, distribute, and rotate encryption keys entirely offline — ensuring critical infrastructure is never exposed.
Streamlined Compliance for OT Key Management
Simplify compliance and reduce manual overhead. AKMSecure automates provisioning, renewal, and revocation of keys across OT devices — helping meet global standards.
AKM for Any OT Platform
Scale securely across your infrastructure. Our modular, API-driven solution integrates into any OT stack — with minimal processing overhead and no PKI complexity.
Ready to Secure Your OT Future?
Discover how AKMSecure can protect your industrial systems. Request a demo or connect with our team to explore deployment and partnership opportunities.
Request a Demo